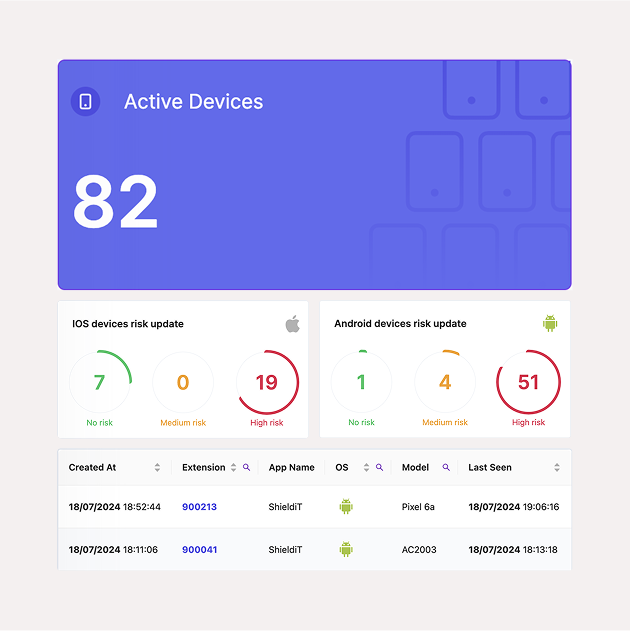
"We have been working with Assac Networks ShieldiT Solution, offering it to our corporate clients as Cyber Defense solution for both hacking and tapping prevention. We have a lot of experience and are aware of the solutions, (some of which we are no longer promoting since we shifted to ShieldiT), for end point security in the corporate markets, and found ShieldiT to be satisfactory to cover both threats in a simple straight forward way, integration was very quick and working with the ManageiT helps corporate CiSOs, our clients a lot. Assac Networks have been supportive and reacted to our needs and complaints, we strongly recommend Using ShieldiT."
CEO and Founder, TAG
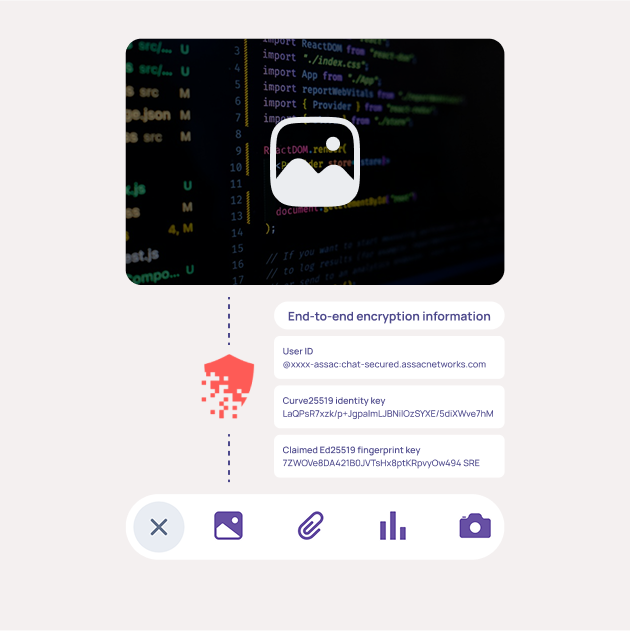
"This is to confirm that our corporate has recently purchased the ShieldiT solution from Assac Networks in its multi-tenant version, we also have our own ManageiT Dashboard to cover our end point security needs. We were looking for a hacking and tapping protection mix and found it in the product, and since it was implemented the company has supported us to our satisfaction. The implementation of this product was successfully finished end of 2019, and we are satisfied from the product in terms of the encryption capability and cyber protection. We strongly recommend this product and we plan to extend its usage in our corporate in the near future."
CISO, AroundTown
"This is to confirm that Assac Networks had provided professional services to Elbit Systems – C4I & Cyber. The services were provided professionally, on time and to our full satisfactory. We strongly recommend working with Assac Networks."
Director of Planning, Elbit Systems